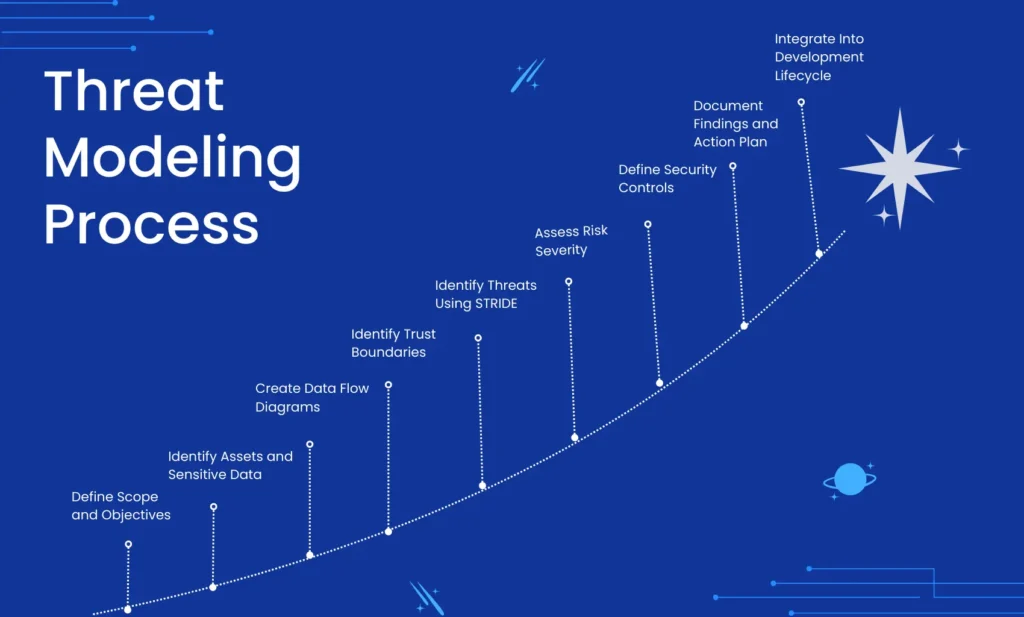
The Threat Modeling Process is a structured approach to identifying, assessing, and mitigating security risks in applications and systems. By following a step by step threat modeling process, organizations can proactively reduce vulnerabilities and strengthen their secure SDLC strategy.
Step 1: Define Scope and Objectives
Start by clearly defining. This phase typically aligns with a formal application security architecture review to ensure design-level risks are identified early.
• Application name and version
• Business purpose
• Environment such as production or staging
• Compliance drivers such as ISO 27001, NIST, PCI DSS
Determine what is in scope:
• Web frontend
• Backend services
• APIs
• Authentication provider
• Cloud resources
Output of this step: A clearly documented scope statement.
Step 2: Identify Assets and Sensitive Data
Identify what needs protection:
• Customer data
• Payment information
• Authentication tokens
• Session cookies
• Source code
• API keys
• Admin functionality
Classify data based on sensitivity. This enables proper risk prioritization.
Step 3: Create Data Flow Diagrams
A Data Flow Diagram illustrates:
• External users
• Web servers
• Application servers
• Databases
• Third party integrations
• Data movement between components
Include trust boundaries such as:
• Internet to web server
• Web tier to internal network
• Application to database
• Cloud to on premise systems
A clear DFD is foundational for accurate threat identification.
Step 4: Identify Trust Boundaries
Trust boundaries represent changes in privilege level or control domain.
Examples:
• Public user to authenticated user
• Web application to database
• Application server to cloud storage
• Internal service to external API
Threats frequently emerge at boundary crossings.
Step 5: Identify Threats Using STRIDE
The STRIDE model is commonly used in web application threat modeling. The OWASP community provides structured guidance on implementing threat modeling in modern application environments.
S Spoofing
T Tampering
R Repudiation
I Information Disclosure
D Denial of Service
E Elevation of Privilege
For each component and data flow in your DFD, ask:
• Can identity be spoofed
• Can data be modified
• Can actions be denied
• Can sensitive data leak
• Can availability be disrupted
• Can privilege escalation occur
Document identified threats in a structured risk register.
Step 6: Assess Risk Severity
Use a risk rating model such as:
• Likelihood versus Impact
• DREAD
• CVSS adapted for design phase
Evaluate:
• Business impact
• Exploitability
• Exposure surface
• Regulatory impact
Categorize risks as High, Medium, or Low.
Step 7: Define Security Controls
Map threats to mitigation strategies such as.
• Strong authentication and MFA
• Role based access control
• Input validation and output encoding
• Secure session management
• Encryption at rest and in transit
• Logging and monitoring
• Rate limiting and throttling
• Secure configuration baselines
Align controls with standards like OWASP ASVS and ISO Annex A where applicable.
These mitigations should be validated through structured secure code review services to ensure vulnerabilities are not introduced during implementation.
Step 8: Document Findings and Action Plan
A professional threat modeling report should include:
• Executive summary
• Architecture overview
• Data flow diagrams
• Threat list
• Risk ratings
• Recommended controls
• Remediation roadmap
This document becomes a living artifact integrated into the Secure SDLC.
Step 9: Integrate Into Development Lifecycle
Threat modeling should not be a one time activity.
Best practice integration:
• During architecture design reviews
• Before major feature releases
• During cloud migration
• When adding third party integrations
• After significant code refactoring
Embedding threat modeling into DevSecOps pipelines ensures continuous risk reduction. Organizations seeking structured implementation support often formalize this process through dedicated threat modeling services integrated into their secure development lifecycle.
Try our free Threat model simulator.
Why the Threat Modeling Process Is Critical for Secure SDLC
Implementing a structured threat modeling process enables teams to identify risks early, prioritize mitigation strategies, and build secure applications by design.
Table of Contents
Need Help Implementing Threat Modeling?
If you’re looking to formalize this process across your organization, our team provides structured threat modeling services aligned with Secure SDLC best practices.