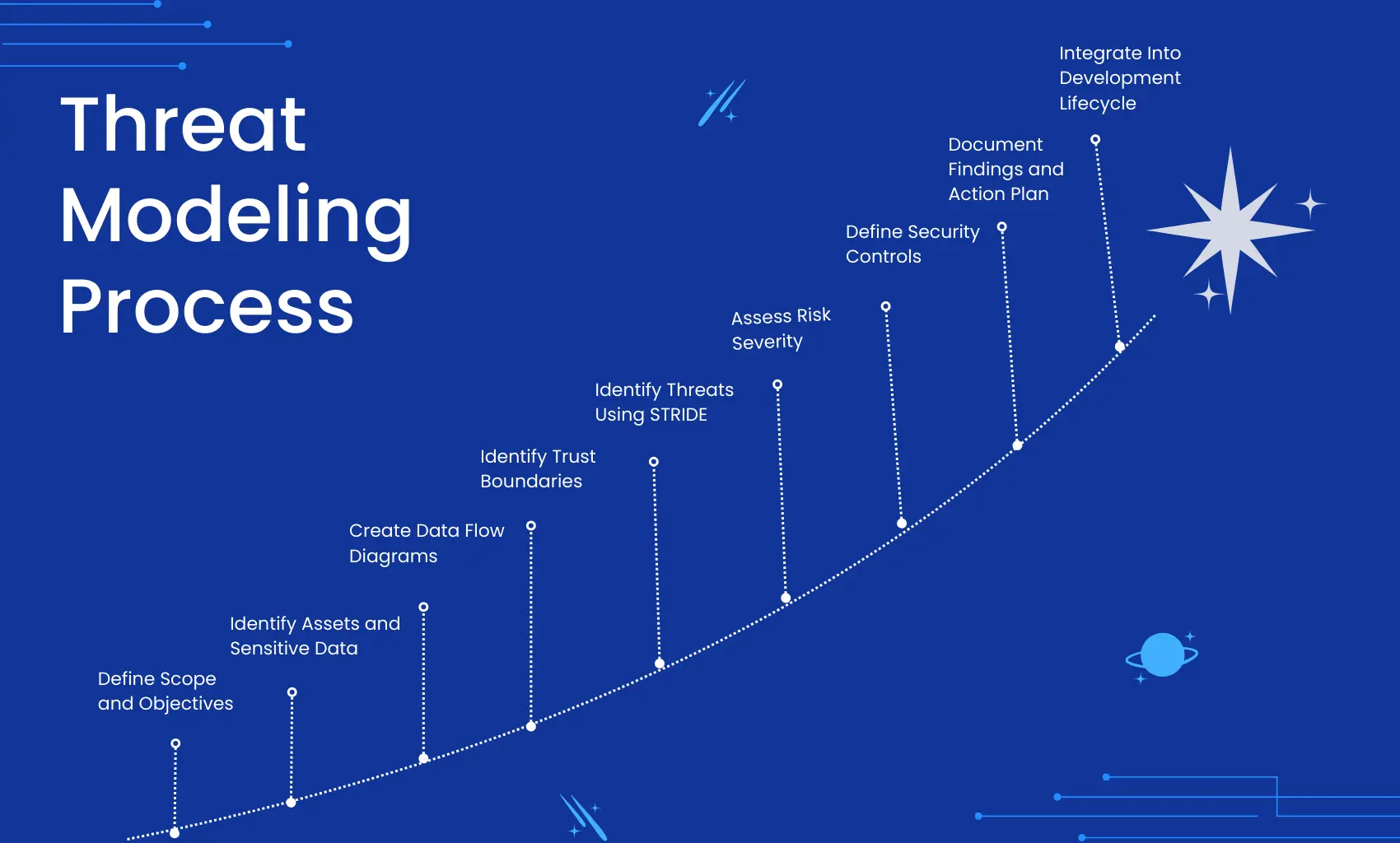
Step by Step Threat Modeling Process
The Threat Modeling Process is a structured approach to identifying, assessing, and mitigating security risks in applications and systems. By following a step by step
Welcome to Secure Wave Advisors. Our mission is simple: to help you build and deploy applications that are safe, compliant, and built to last. With years of cybersecurity experience, we combine technical precision with business insight to protect what matters most your reputation and revenue.
Empowering businesses with secure technology through innovation, expertise, and trusted guidance for digital protection.
To provide unwavering cybersecurity support, enabling businesses to operate safely, confidently, and without disruption.
Secure Wave Advisors: Your dedicated partner in digital defense, safeguarding businesses of all sizes.
Who We Are
At Secure Wave Advisors, we are more than just cybersecurity consultants. We are your dedicated partners in safeguarding your digital world. Our team of experienced ethical hackers, penetration testers, compliance experts, and strategic advisors works tirelessly to protect your business from ever-evolving cyber threats.

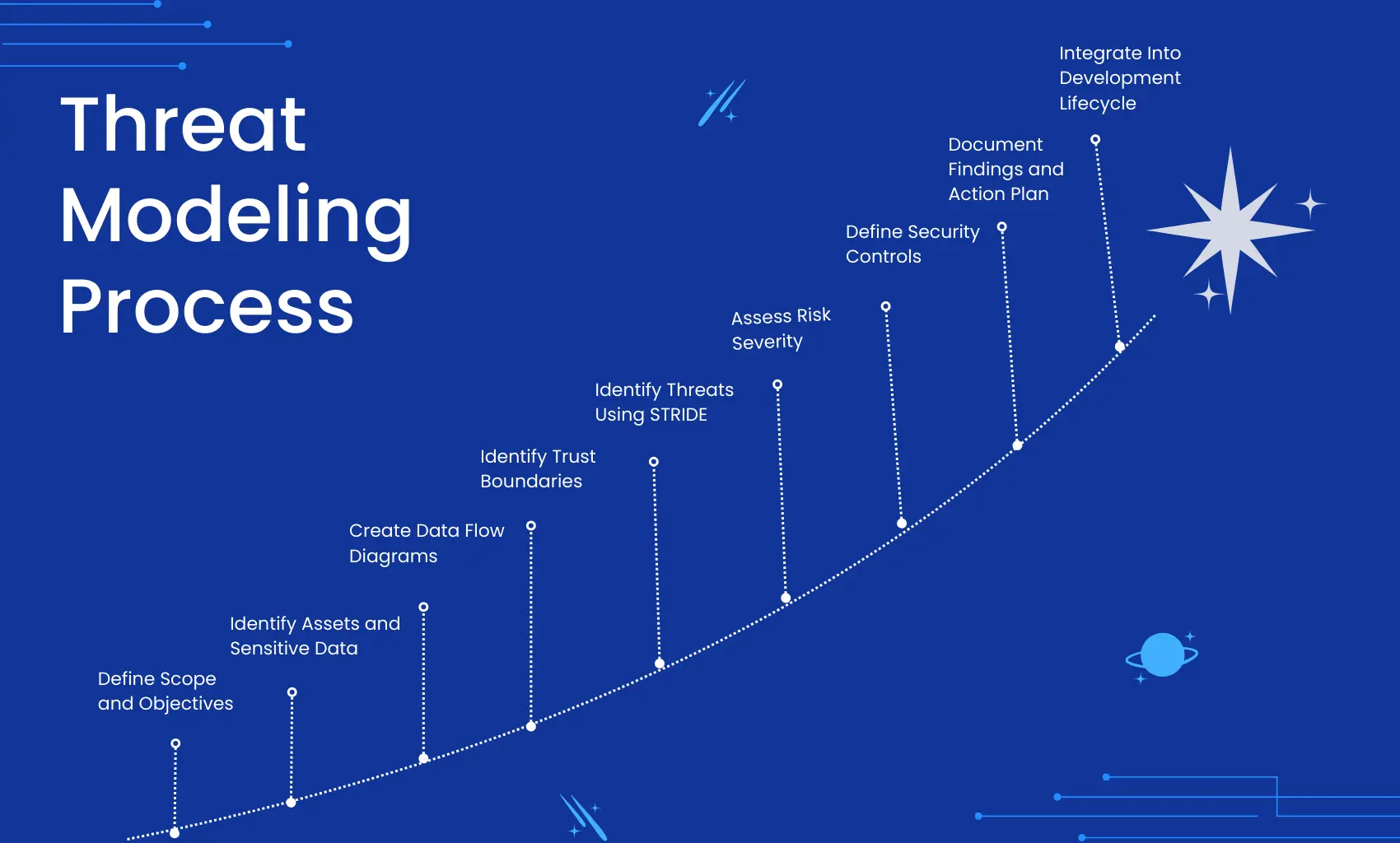
The Threat Modeling Process is a structured approach to identifying, assessing, and mitigating security risks in applications and systems. By following a step by step

Table of Contents Request a free quote Introduction The OWASP Top 10 2025 is here marking the 8th official installment of the industry’s most influential

Table of Contents Request a free quote Static Application Security Testing SAST tools are software solutions that scan an application’s source code to detect security
Certified for Excellence






Stay ahead of cyber threats by learning how Secure Wave Advisors can help protect your business. Discover actionable insights in our latest post on Top SAST Tools for Secure Code a must-read for developers and organizations aiming to write secure software from the start.
What We Offer

Our consulting services help you integrate security into every phase of development. From architecture reviews to secure lag frameworks, we help you build resilient software that stands up to modern threats.

We help you find, prioritize, and fix vulnerabilities before attackers exploit them. Our tailored testing services combine automated scanning with expert manual review for deep analysis.
Why Choose Us
Industry veterans with proven expertise in cybersecurity.
Customized services that meet your business’s unique needs.
Leveraging the latest technologies to protect your assets.
Our process is built on collaboration, transparency, and trust, ensuring you’re informed every step of the way.
Testimonial
Real client experiences reflecting measurable security improvements, technical depth, and trusted advisory partnerships.